The “smart house” concept is becoming the new normal for office buildings, with technology being used to control heating, ventilation, lighting and the opening and closing of doors. But what happens if a cyber criminal manages to gain access to critical systems in the building?
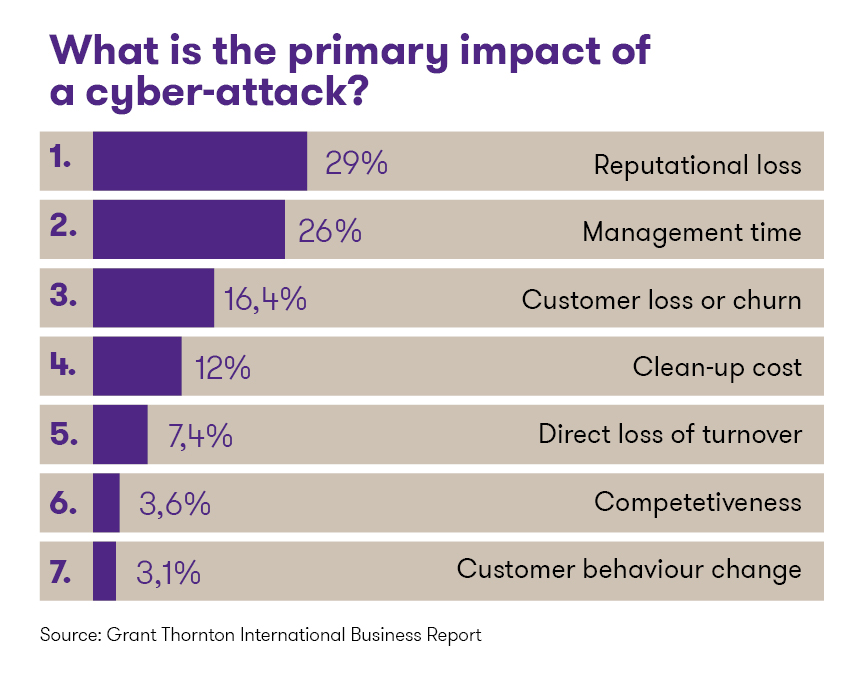
Smart solutions can become a real headache for the owner, if such functions come under the control of a malign influence. An unexpected interruption of service – for example, ventilation and lighting stops working or the power goes out – is a nightmare for any office building, shopping mall or tenant space manager. Besides crippling everyday operations, a cyber attack can also do major damage to reputation. A recent survey conducted by Grant Thornton found that a majority of companies are afraid of precisely the latter consequence of a cyber attack.
Consequently, dealing with cyber security and data protection must be part of daily operating procedure for the management of companies that run an office building, much like analysis of financial reports. That’s unfortunately not the way it is in real life.
The study also revealed that less than 2/3 of companies (65%) have undertaken activities to map what sorts of data are collected in the company, but they don’t know:
- how much data there is,
- what is done with the data and
- what could happen if the data become compromised.
A report from the State Information System Authority (RIA, see https://www.ria.ee/en/) notes that there were 9,135 cases where cyber security was impacted last year in Estonian computer and data communication networks. Of these, 2,248 – about one-fourth – were found to be cyber security incidents, meaning that the event had a direct impact on the confidentiality, integrity or availability of information or systems. The number of cases this year has grown. The question is no longer if we will be hit by a cyber attack – the question is when.
What are the cyber risks?
According to RIA, the most common cyber risks are malware transmitted by e-mail and spread by web domains, and infected and botnet-controlled devices in communication networks. Phishing and ransomware incidents have received greater public attention – the most recent major case involving the latter was in May, when WannaCry spread around the world. The WannaCry virus encrypted files on infected computers, and criminals demanded a ransom in exchange for the “key”. Considering that WannaCry managed to wreak havoc in 150 countries, including Estonia, it is evident that companies must do more to ensure the security of their information systems.
Cyber criminals look for the “door” of least resistance for breaking into companies and seizing control of data and systems. Sometimes this door is located in the supply chain – for instance, a building’s property management company’s IT system might have weak security, giving the criminals access to a company’s systems located in the building. This can come as a very unpleasant surprise for the building tenants who might have been under the impression that everything is fine in terms of security. Every property management company should thus ask themselves whether they have conducted a thorough IT security analysis and adopted appropriate measures to prevent cyber criminals from accessing their information systems. Every tenant who uses the servers, WiFi network and information systems provided by the lessor company should also ask themselves the same question.
How to increase cyber security?
- Determine your company’s business-critical assets: people, buildings, goods and services, processes, databases. 78% of companies establish data protection procedures without evaluating what their valuable data are.
- Make sure you know what every business-critical asset’s greater vulnerability is, and analyse what types of cyber attacks are most likely in this regard: both now and in the future.
- Control systems should be designed to allow employees, supply chain actors and the public (including website visitors) to access only the information they need.
- Keep the networks for tenants and property management company separate whenever this is appropriate and possible.
- Ensure that there is a good reason for any and all accesses to systems and data.
- Back up important data sufficiently frequently and if necessary, update software.
- Encrypt hard drives, set up a properly configured firewall, use anti-virus protection and, if possible, attack detection systems.
- Do not send critical or sensitive data unencrypted by e-mail. At minimum, use encryption.
- Develop a crisis management plan: who does what first, if you come under cyber attack. Test your crisis management plan regularly!
- Make sure all participants in the supply chain know their duties in ensuring cyber security – every link in the chain is connected to others, too!
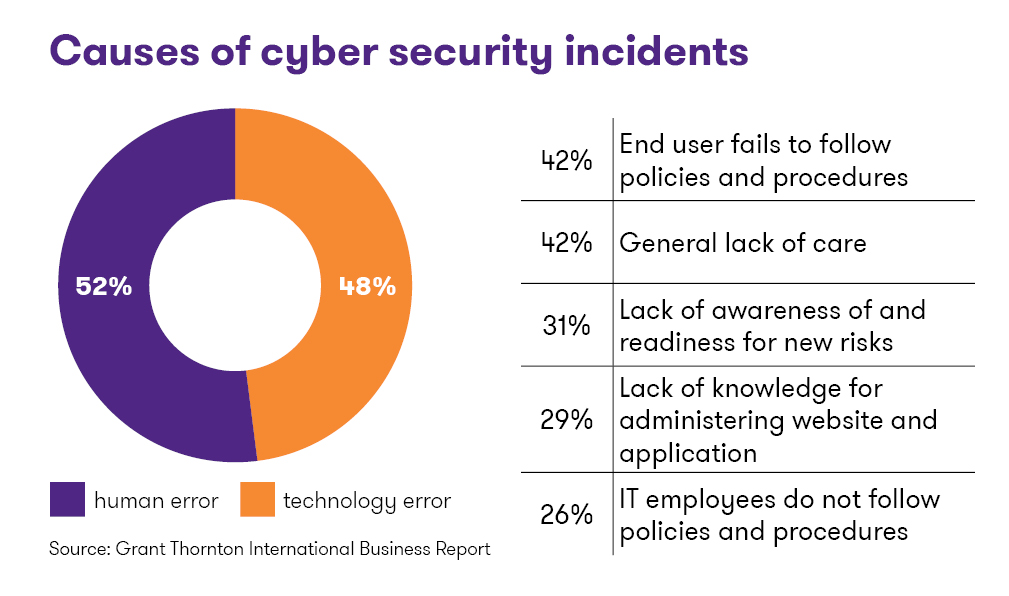
- Place special emphasis on raising employee awareness, as people are the weakest link in ensuring cyber security. There will always be someone who, because they don’t know better or weren’t thinking, clicks on a link in an e-mail and infects a computer with malware. Make training employees on IT security topics something your company does on a consistent basis.
Author: Siiri Antsmäe
